Less than a year ago we published an article about how virtual reality would soon challenge the world we live in. Some of the challenges companies like Oracle have been facing included creating a virtual reality that we can smell, taste, touch, and hear.
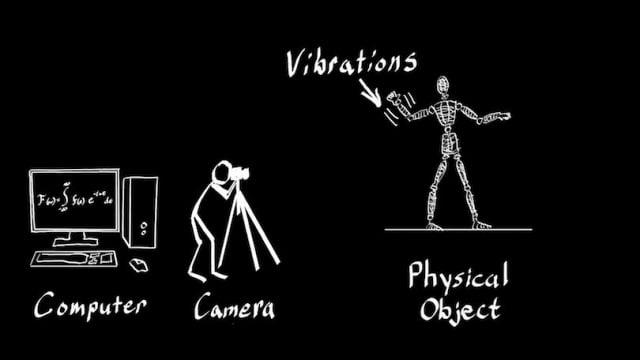
While giant tech companies still have to work on to face most of today’s challenges, MIT Computer Science and Artificial Intelligence Laboratory (CSAIL) researchers have achieved a new goal: the ability to touch objects inside videos. Intelligently using algorithms and affordable camera technology, MIT researchers have created video simulations by finding object natural vibrations that can easily hep users interact with the video and make them feel like they are touching a specific object by bending and stretching it as they like.
“This technique lets us capture the physical behavior of objects, which gives us a way to play with them in virtual space,” according to CSAIL PhD student Abe Davis. “By making videos interactive, we can predict how objects will respond to unknown forces and explore new ways to engage with videos,” Davis added.
Many companies are already using very expensive camera equipments and Computer-generated imagery (CGI) to achieve the desired results. But what if you need to make a movie on a budget and don’t have the luxury of having expensive camera equipment and cannot afford CGI effects?
MIT’s ‘Interactive Dynamic Video’ from now on will give filmmakers the opportunity to produce any visual effects they want without feeling limited to do so.
“Called the ‘Interactive Dynamic Video (IDV)’, this technology makes it possible for humans (and cartoons) to physically interact with photos and videos. In other words, you can poke, prod and push the things you see in the videos, MIT News reports. [...] IDV has many possible uses, from filmmakers producing new kinds of visual effects to architects determining if buildings are structurally sound, said Davis,” according to techworm.net.
Last May, researchers at the Massachusetts Institute of Technology developed a new software that can identify in a quick and (almost) accurate way any flaws regarding the security of Web applications that are written in Ruby on Rails (RoR).
According to Daniel Jackson, a professor in the Department of Electrical Engineering and Computer Science, MIT’s new developed system uses static analysis technique, which generally describes the way data flows through a program.
Daniel Jackson along with University of California at Berkeley researcher Joseph Near, after testing 50 popular Web apps written in RoR discovered 23 security flaws that were previously unknown spending no more than 63 seconds inspecting each app in particular.
“Even if you wrote a small program, it sits atop a vast edifice of libraries and plug-ins and frameworks. So when you look at something like a Web application written in language like Ruby on Rails, if you try to do a conventional static analysis, you typically find yourself mired in this huge bog. And this makes it really infeasible in practice,” according to Jackson.